We are fighting a 21st-century war with 19th-century bureaucracy.
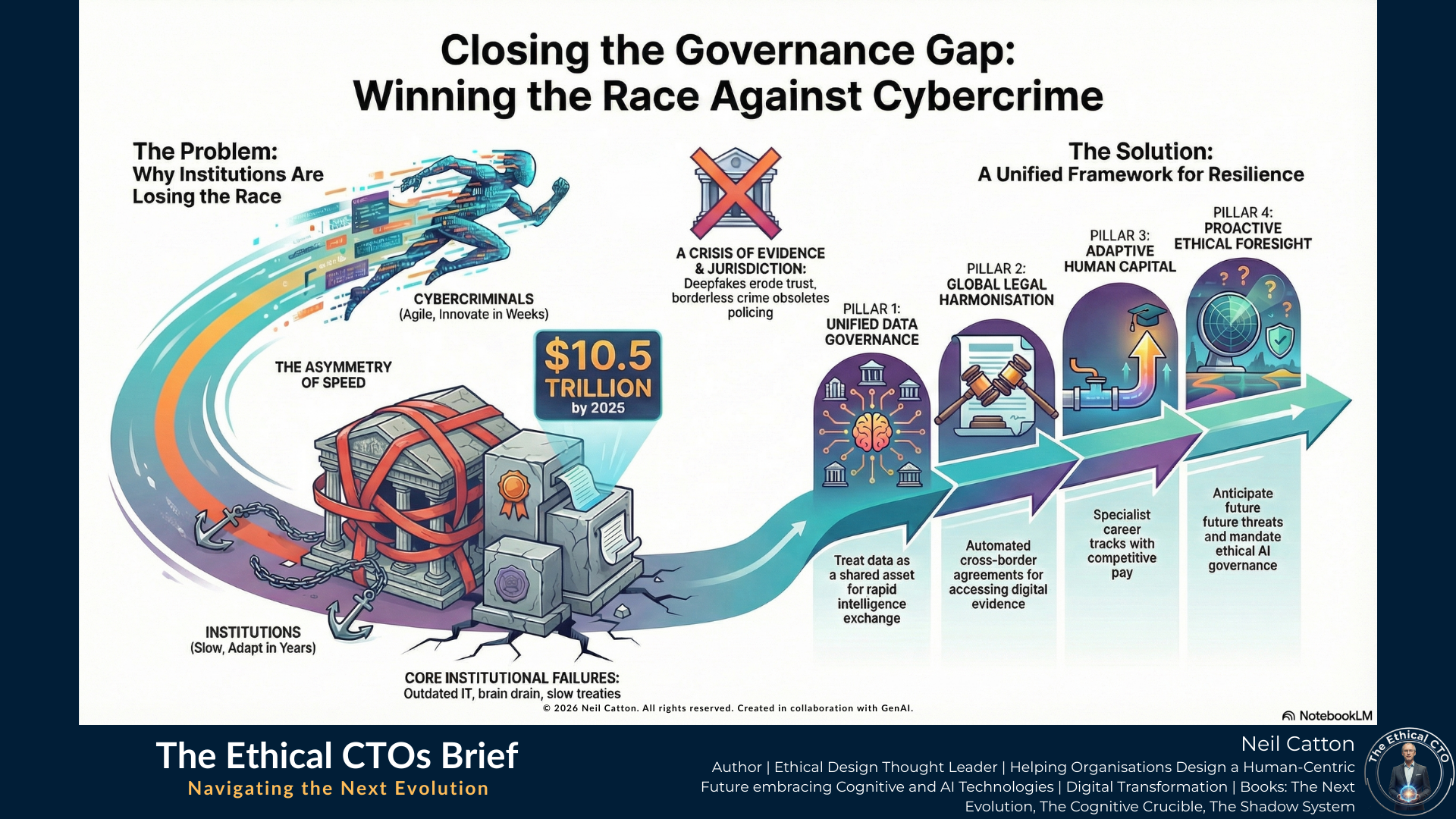
Right now, there is a massive disconnect between how fast cybercriminals move and how slowly our institutions respond. While digital syndicates operate like agile, AI-powered startups, iterating in weeks, our legal and law enforcement frameworks often adapt over years.
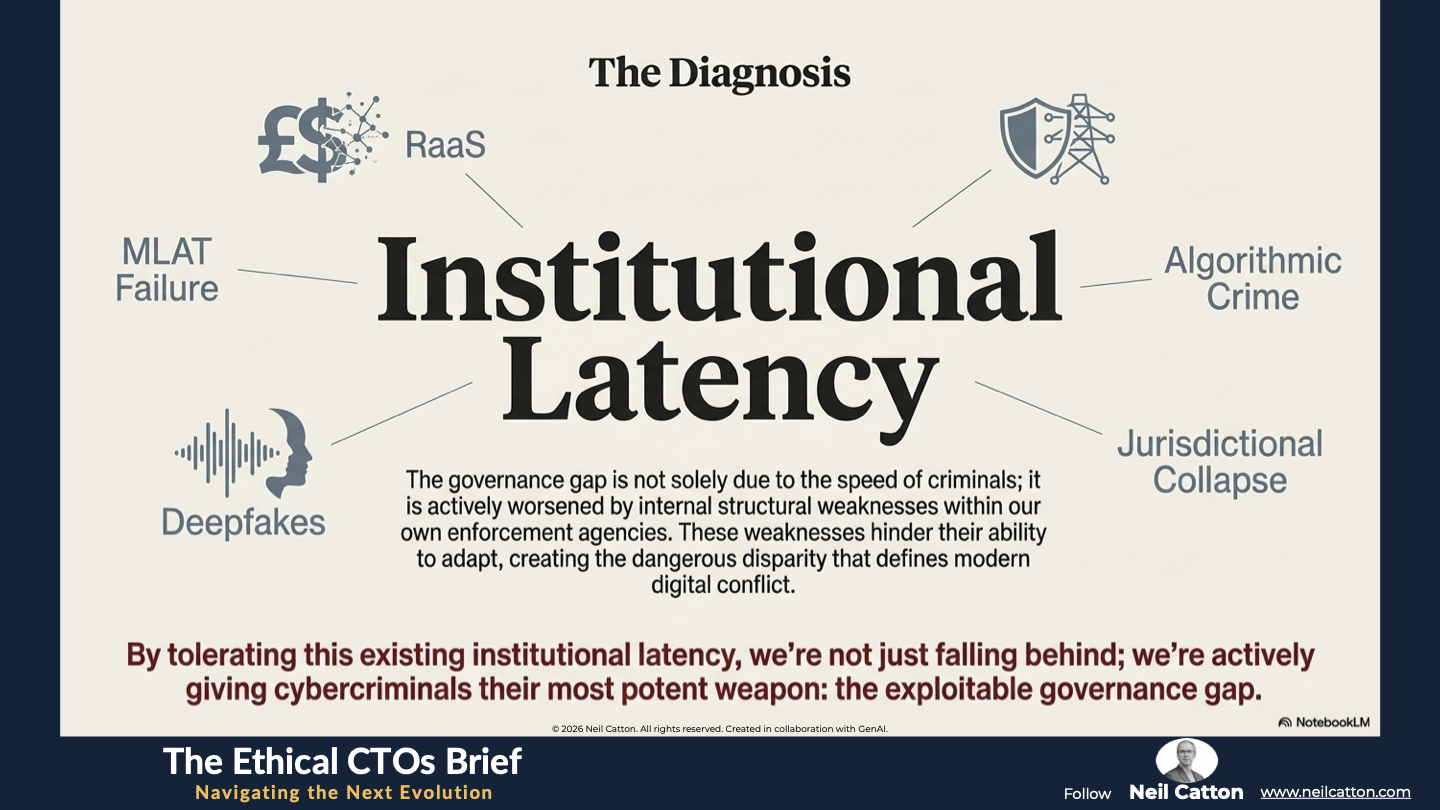
I call this "Institutional Latency," and it is currently the greatest weapon in the cybercriminal’s arsenal. In Closing the Governance Gap, I examine why our traditional approach to digital security is failing and how we can architect a more resilient future. This isn't just a technical problem; it’s a structural one. We need to move away from reactive "digital policing" and toward a model of proactive, systemic governance that can actually keep pace with the threat.
The article explores:
The Asymmetry of Speed: Why agility is the new frontline of national security.
Institutional Latency: The hidden cost of bureaucratic delay in a hyper-connected world.
Proactive Defence: Moving toward a technologically agile governance model that secures our digital future.
If we don't bridge the gap between our tech and our oversight, we aren't just falling behind, we’re leaving the door wide open.
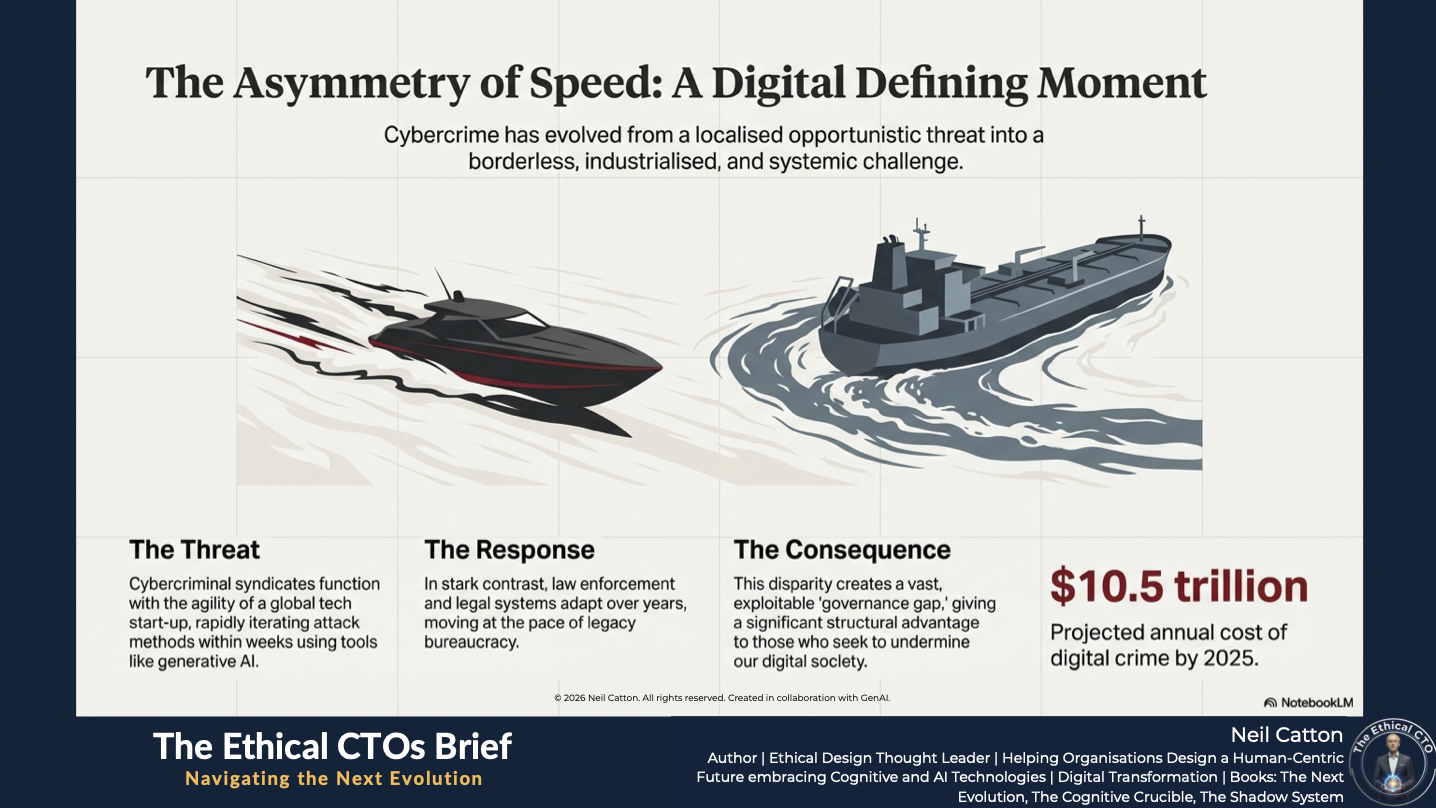
The Asymmetry of Speed: A Digital Defining Moment
Cybercrime has evolved from a localised opportunistic threat into a borderless industrialised and systemic challenge. This poses a significant threat to national security and global economic stability. This isn’t hyperbole; digital crime costs are projected to reach a staggering $10.5 trillion annually by 2025. While this immense financial impact highlights the damage, the true crisis lies in the Asymmetry of Speed that defines modern digital conflict.
Today’s cybercriminal syndicates function with the agility and responsiveness of a highly funded global tech start-up. They rapidly iterate their attack methods within weeks using cutting-edge tools like generative AI. In stark contrast, law enforcement and legal systems often move at the pace of legacy bureaucracy, adapting to new digital threats over years. This dangerous disparity, which I call Institutional Latency, currently gives those who seek to undermine our digital society a significant structural advantage. It creates a vast exploitable governance gap.
This article goes beyond simply outlining the technical threats posed by ransomware and phishing. It provides a vital diagnosis of the systemic failures that allow these threats to thrive. Furthermore, it proposes a new unified framework to close this dangerous governance gap and build lasting structural cyber resilience.
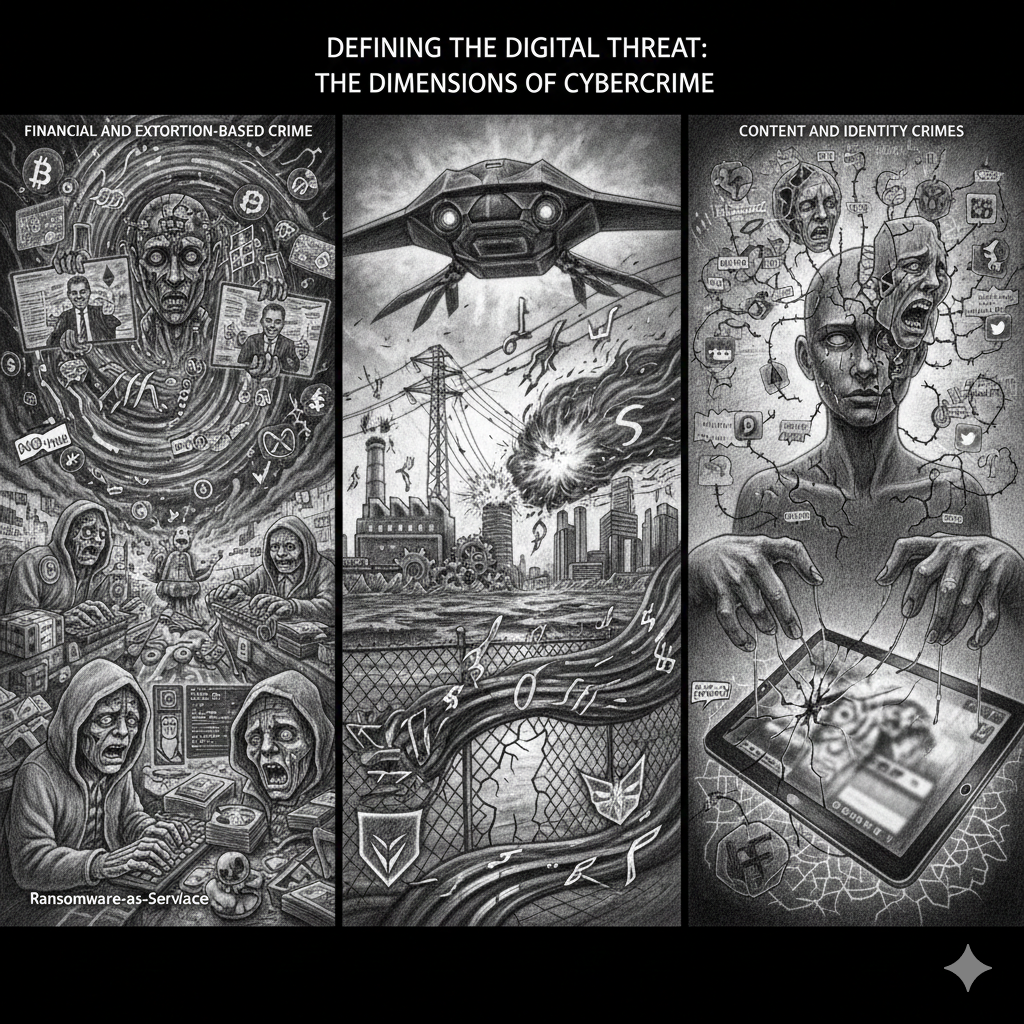
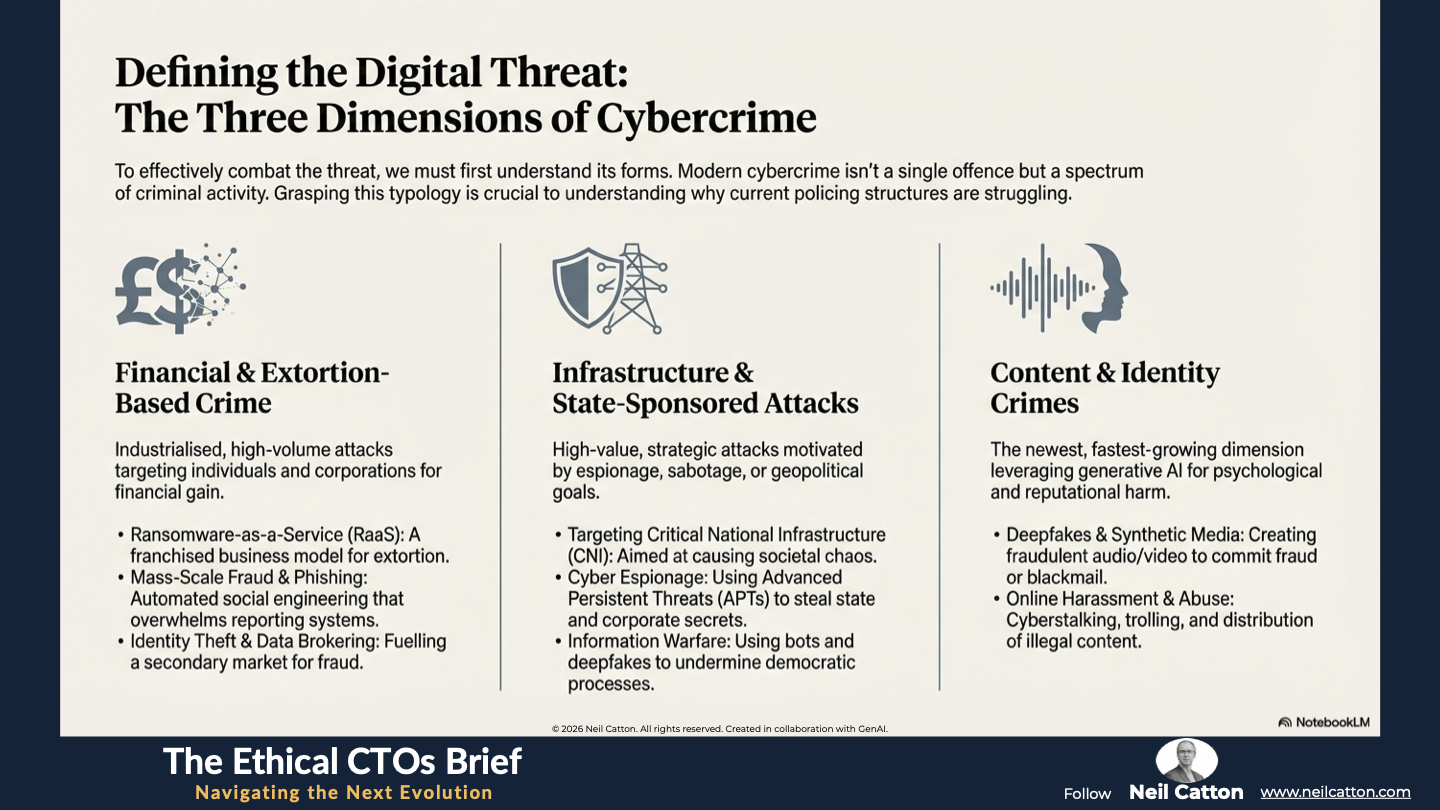
Defining the Digital Threat: The Dimensions of Cybercrime
To effectively combat a threat, we must first understand its various forms. Modern cybercrime isn’t a single offence but a spectrum of criminal activity utilising digital technology throughout its lifecycle - from planning and execution to obfuscation and laundering. It’s best understood across three key dimensions, each necessitating a fundamentally different policing approach.
Dimension A: Financial and Extortion-Based Crime
This dimension encompasses the most significant volume of incidents and directly targets individuals and corporations for financial gain. It has become industrialised, driven by professional and highly organised criminal networks that function like efficient businesses.
- Ransomware-as-a-Service (RaaS): The model has shifted from simple hacking to a sophisticated, franchised business where developers create malicious code and 'sell' its use to affiliates who execute the attacks, often culminating in the encryption of data and the threat of public release (double extortion).
- Mass-Scale Fraud and Phishing: Automated tools are used to deploy highly believable social engineering attacks, including Business Email Compromise (BEC) and sophisticated investment scams, overwhelming existing police reporting systems through sheer volume.
- Identity Theft and Data Brokering: The illegal trade of stolen personal data, credentials, and financial information on the dark web, fuelling a secondary market for identity-related fraud.
Dimension B: Infrastructure and State-Sponsored Attacks
This dimension targets high-value, strategic assets, often motivated by espionage, sabotage, or geopolitical goals. These attacks are typically characterised by their complexity, persistence, and backing by state-level resources:
- Targeting Critical National Infrastructure (CNI): Attacks aimed at disrupting essential services such as power grids, financial systems, healthcare networks, and transportation. These are often not financially motivated but designed to cause widespread societal chaos and instability.
- Cyber Espionage: Sophisticated campaigns, often using Advanced Persistent Threats (APTs), to steal intellectual property, classified government data, and sensitive diplomatic information from public and private sectors.
- Information Warfare: The deployment of digitally driven campaigns (via bots, social media manipulation, and deepfakes) to undermine democratic processes, erode public trust, or influence foreign policy.
- Deepfakes and Synthetic Media: The use of AI to create hyper-realistic fraudulent audio, video, or documents to commit fraud, blackmail, or reputational damage. This directly impacts the integrity of evidence.
- Online Harassment and Abuse: Non-physical crimes executed via digital means, including cyberstalking, trolling, and the distribution of illegal content, often impacting vulnerable individuals.
Dimension C: Content and Identity Crimes
The newest and fastest-growing dimension leverages generative AI and digital platforms to commit crimes related to psychological harm, identity, and moral integrity:
Grasping this typology – from financial fraud to state-level espionage and identity abuse – is crucial. It immediately explains why current policing structures, designed for traditional territorial crimes, are struggling to handle the scale and complexity of the new digital landscape.
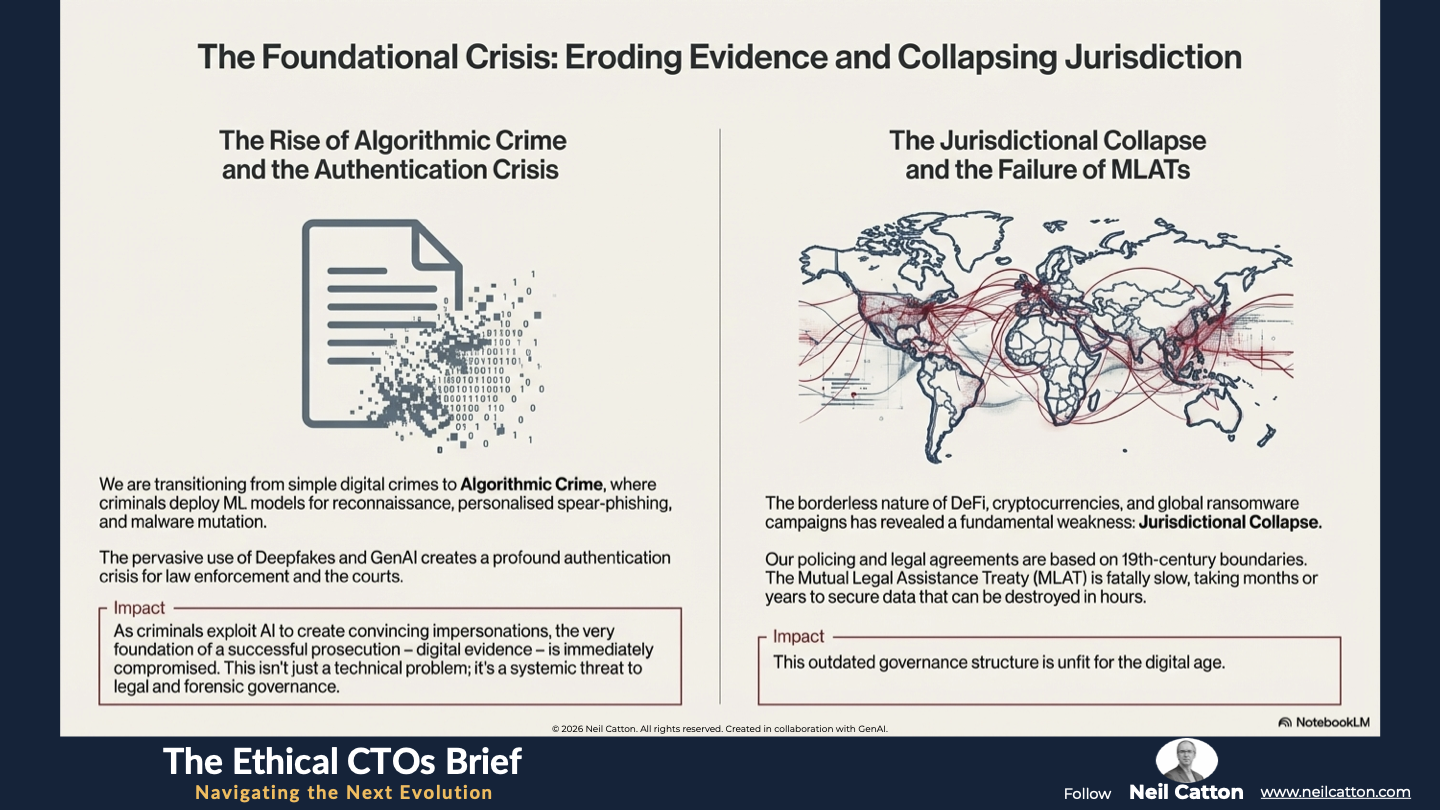
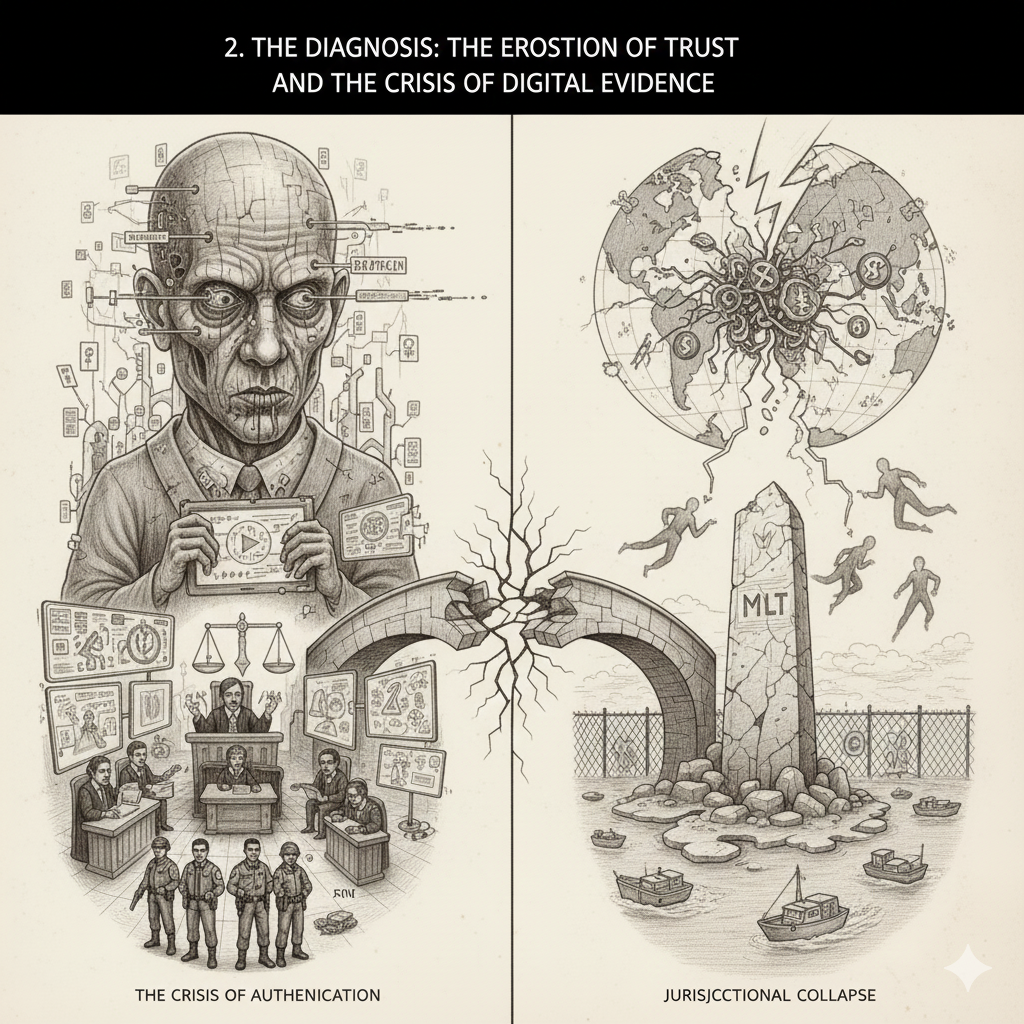 The Erosion of Trust and the Crisis of Digital Evidence
The Erosion of Trust and the Crisis of Digital Evidence
To truly grasp the institutional challenge, we must first acknowledge how sophisticated cyber threats are fundamentally undermining two key pillars of law enforcement: the ability to locate, authenticate, and successfully prosecute digital evidence across any jurisdiction. This diagnosis highlights the immense technological and jurisdictional burdens currently facing police forces and serves as a crucial precursor to comprehending the necessity for structural reform.
Algorithmic Crime and the Authentication Crisis
We’re rapidly transitioning from simple digital crimes to Algorithmic Crime involving sophisticated machine learning (ML) models deployed by criminals for more than just executing attacks. They’re used for initial reconnaissance, generating hyper-personalised phishing campaigns, and mutating malware to evade traditional signature-based detection systems. The scale is industrial and the precision unprecedented.
The challenge facing the justice system stems from Deepfakes and advanced GenAI. This pervasive deployment of synthetic media presents a profound crisis for law enforcement and the courts, raising serious questions about authentication. As criminals exploit AI to create convincing audio and video impersonations of executives, key witnesses and victims, the very foundation of a successful prosecution – digital evidence – is immediately compromised. If police can’t reliably distinguish between real and synthetic content or if forensic resources are stretched thin, taking months to deploy, the criminal justice system faces paralysis. This isn’t just a technical problem; it’s a systemic threat to legal and forensic governance.
The Jurisdictional Collapse and the Failure of MLATs
The anonymous and borderless nature of decentralised finance (DeFi) and cryptocurrencies, combined with the rapid and non-territorial deployment of attacks like global ransomware campaigns, has revealed a fundamental weakness in global policing: Jurisdictional Collapse.
Crime persists in the digital world, but our policing, legal, and international agreements are still based on 19th-century boundaries. The Mutual Legal Assistance Treaty (MLAT), the main way to share evidence across borders, is slow and often takes months or even years to secure crucial data. This delay is fatal when a crime can be carried out, laundered across three continents through multiple cryptocurrency wallets, and evidence destroyed within hours. This outdated governance structure is unfit for the digital age. Police forces urgently need trusted and legally harmonised data access protocols, moving away from slow diplomatic instruments towards automated judicially sanctioned data-sharing agreements.
The Institutional Challenge: Policing's Latency Crisis
Having established the severity of the threat landscape and the resulting evidence crisis, we must now focus on addressing the root cause of the governance gap. The institutional lag isn’t solely due to criminals; it’s actively worsened by internal structural weaknesses within enforcement agencies. These weaknesses hinder their ability to adapt quickly, ultimately giving criminals an advantage.
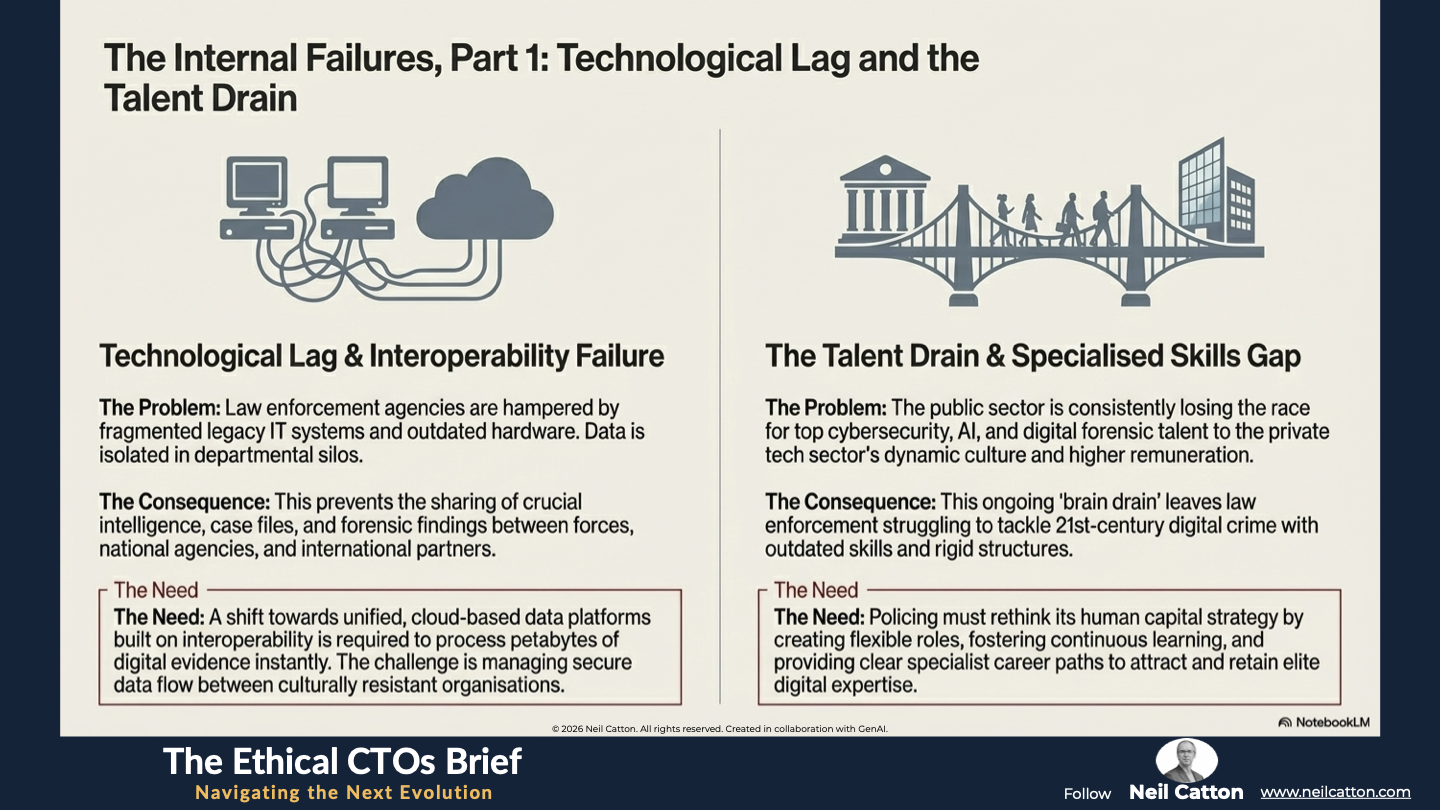
Technological Lag and Interoperability Failure
Law enforcement agencies worldwide face significant challenges due to fragmented legacy IT systems. Data is isolated within departments and relies on outdated hardware that can’t support modern tools. This leads to interoperability failures, preventing forces from sharing crucial intelligence, case files, and forensic findings with neighbouring forces, national agencies, or international partners.
To effectively tackle large-scale algorithmic crime, police need to ingest and process petabytes of digital evidence almost instantly. This demands a significant and expensive shift towards unified cloud-based data platforms built on interoperability as a fundamental principle rather than an optional feature. Ultimately, the key challenge isn’t simply purchasing new technology but managing secure and transparent data flow between multiple often culturally resistant organisations.
The Talent Drain and the Specialised Skills Gap
The race for top cybersecurity, AI, and digital forensic talent is intense, and the public sector is consistently losing out. Public sector salaries and career structures don’t match the agile private tech sector’s dynamic culture, challenging projects, and generous remuneration. This ongoing ‘brain drain’ leaves law enforcement struggling to tackle complex 21st-century digital crime with outdated skills and rigid organisational structures.
The skills gap is worsened by the lack of clear modern specialist career paths. There’s often no formal way to recognise and reward the unique technical expertise needed to investigate complex deep-state cyber espionage and algorithmic fraud cases. To address this, policing must rethink its human capital strategy. This involves creating flexible roles, fostering continuous learning environments, offering non-traditional incentives, and providing clear progression paths. These measures will attract and retain the elite digital expertise required.
The Ethical and Moral Foresight Deficit
Law enforcement has a responsibility not only to respond to immediate threats but also to anticipate and plan for future ones emerging from the technological future. Currently, there’s a substantial moral foresight deficit in forward-thinking planning for truly disruptive technologies that could undermine current policing capabilities.
For example, the imminent commercialisation of quantum computing poses a devastating existential threat. Once viable quantum computers become widely accessible they will be able to break most public-key encryption standards globally, including those safeguarding government data communications and all historical digital evidence. Therefore, policing must proactively mandate and initiate the resource-intensive transition to Post-Quantum Cryptography (PQC) standards now. Failure to do so will result in a near-future where all historical and newly collected digital evidence becomes vulnerable. Similarly, the deployment of police AI tools like predictive analytics must be governed by robust ethical frameworks to prevent algorithmic bias and protect fundamental civil liberties. This is crucial for maintaining public trust in policing, which is essential for effective law enforcement.
A Unified Framework for Structural Cyber Resilience
Addressing institutional latency and closing the governance gap requires a radical systematic response centred on building structural resilience. We need to transition from reactive investigation to proactive governance by establishing a unified four-pillar framework specifically designed to outpace the criminal threat. This framework must be implemented simultaneously to create a stable foundation for the digital future.
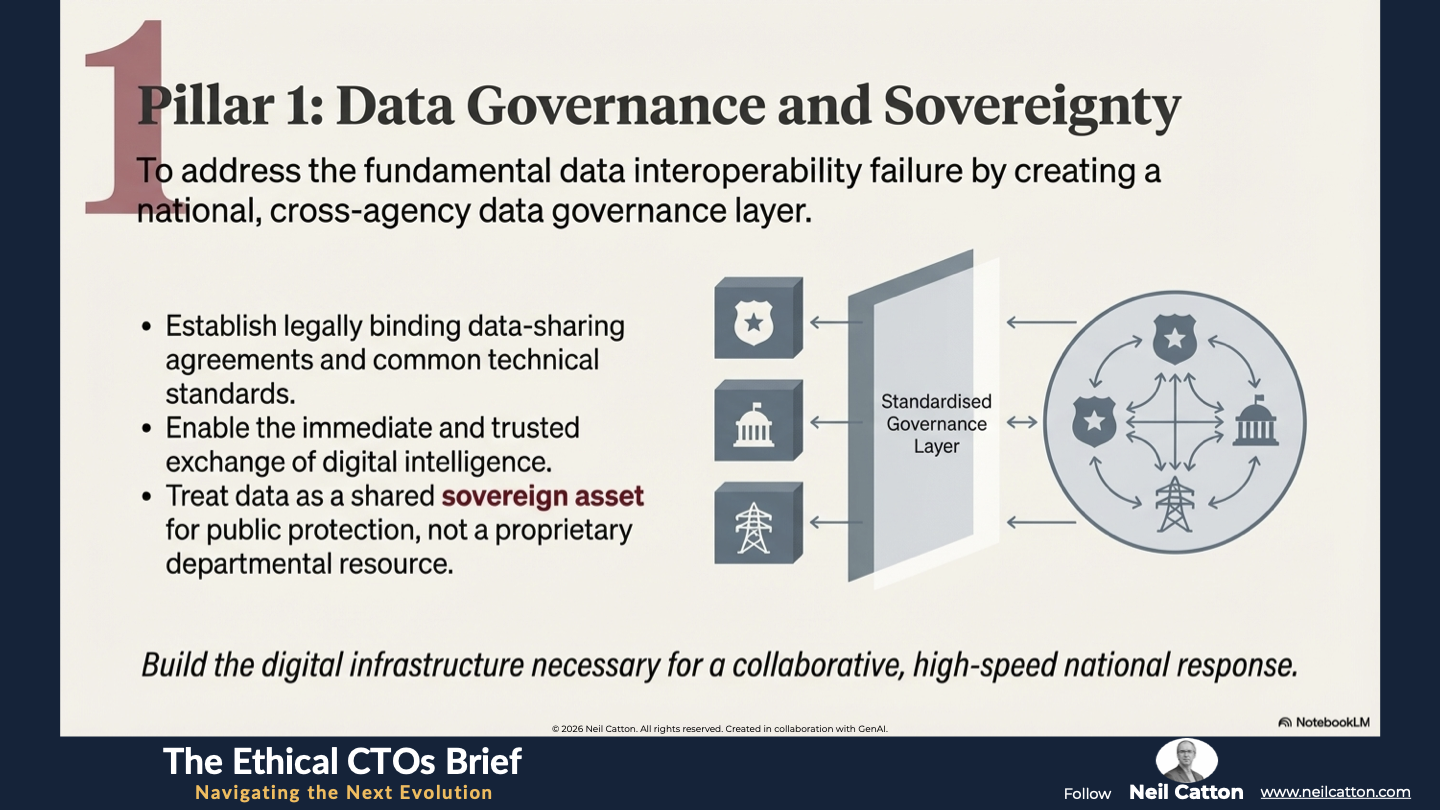
Pillar 1: Data Governance and Sovereignty
The core mandate is to address the fundamental data interoperability failure. This involves creating a national, cross-agency data governance layer. This layer will be supported by legally binding data-sharing agreements and common technical standards. These standards will enable the immediate and trusted exchange of digital intelligence between police, national intelligence services, and critical national infrastructure providers. Data should be treated as a shared sovereign asset rather than a proprietary departmental resource. This requires unified high-speed access for public protection. Ultimately, this is about building the digital infrastructure necessary for a collaborative response.
Pillar 2: Global Legal Harmonisation
We must acknowledge the limitations of MLATs and move beyond them. Our focus should shift decisively to harmonising digital evidence law. This involves driving international diplomatic and judicial agreements that standardise the collection, preservation and presentation of digital evidence in court across different jurisdictions. The goal is to facilitate automated, rapid, and legally sound cross-border access to cloud-stored data irrespective of the server’s location. This is a crucial political and diplomatic imperative that directly addresses the non-territorial nature of modern algorithmic crime.
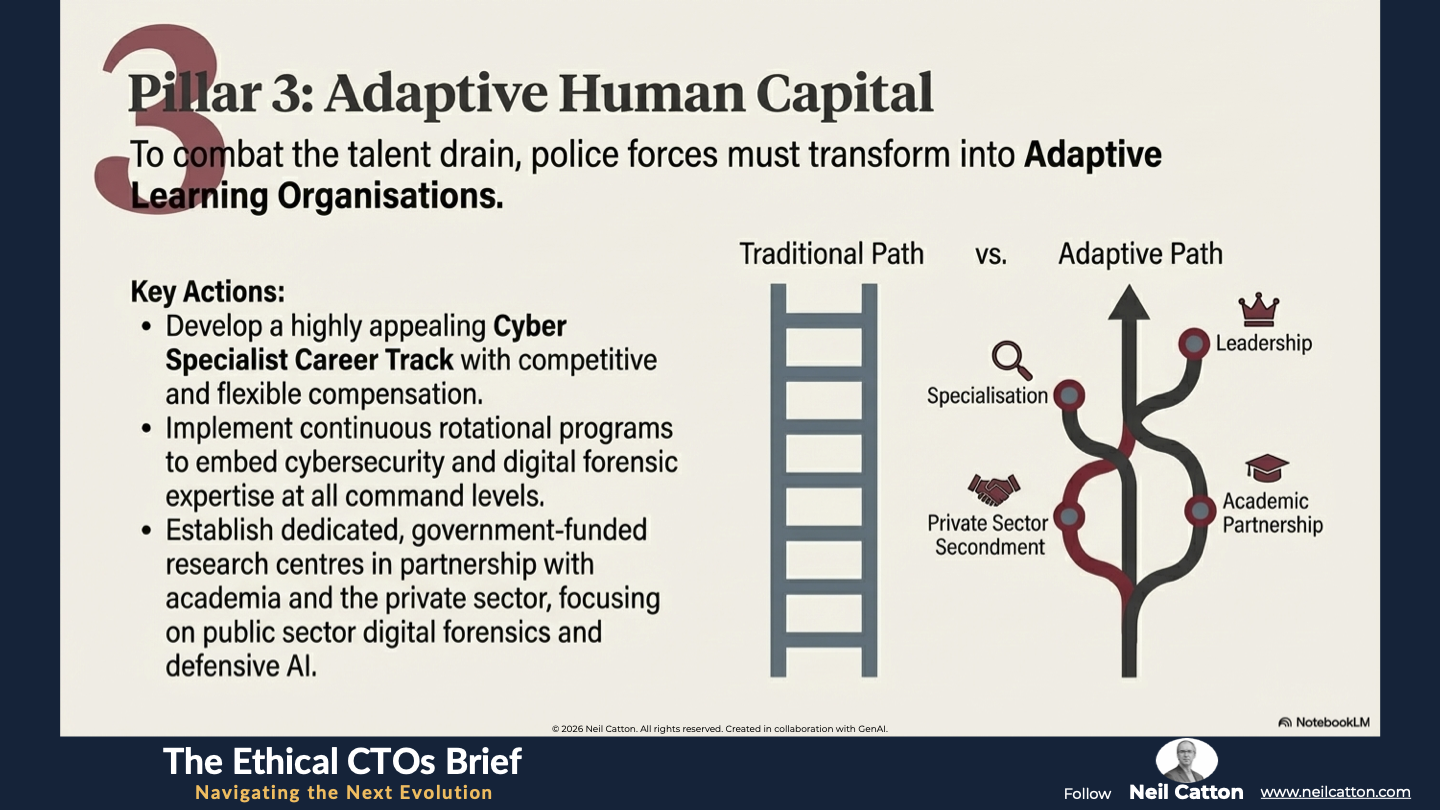
Pillar 3: Adaptive Human Capital
To combat the talent drain, police forces must transform into Adaptive Learning Organisations. This involves developing a highly appealing Cyber Specialist Career Track with competitive and flexible compensation. Additionally, continuous rotational programs should embed cybersecurity and digital forensic expertise throughout all command levels from frontline officers to senior leadership. Building sovereign capability requires partnerships with academia and the private sector to establish dedicated government-funded research centres. These centres should focus on public sector digital forensics defensive AI and ethical governance tools.
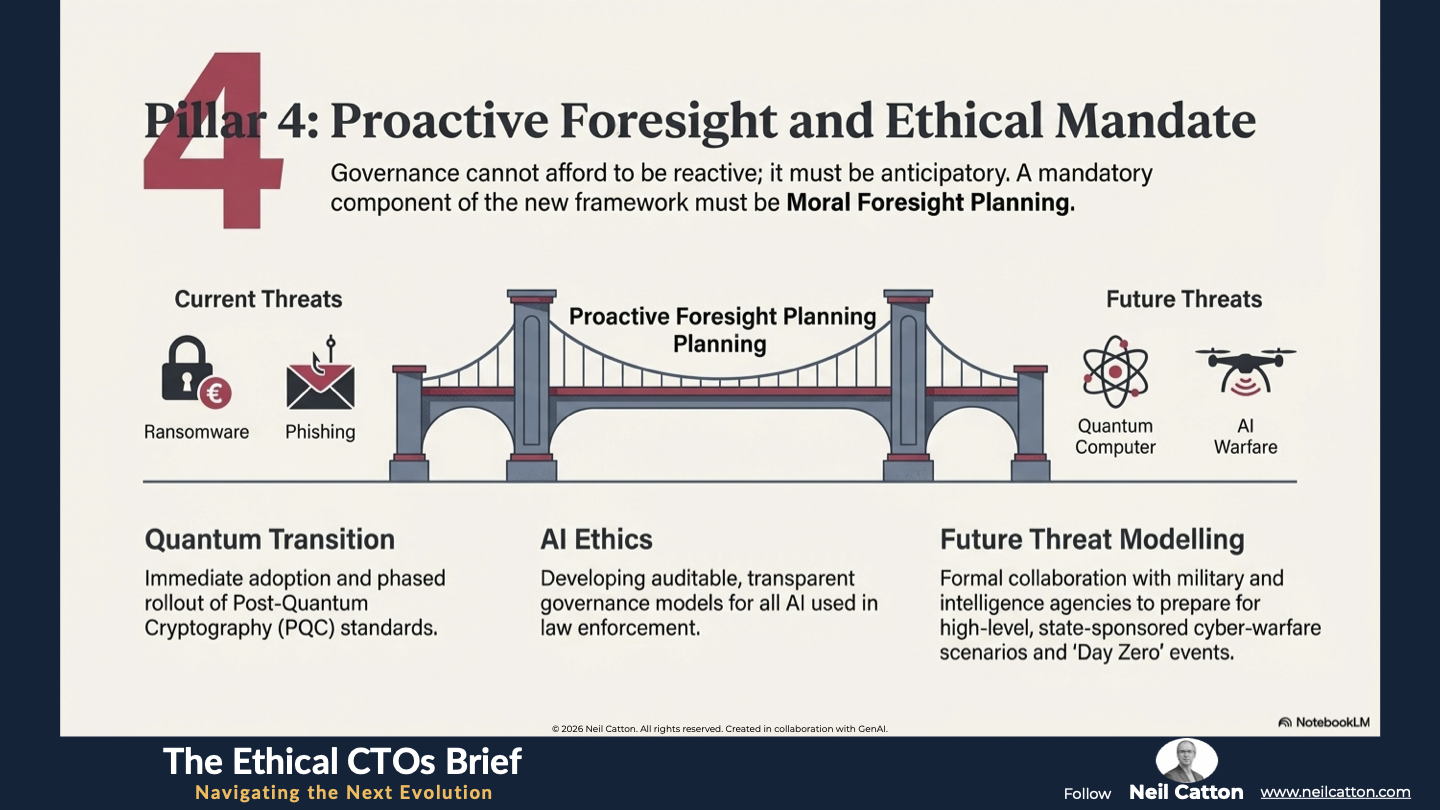
Pillar 4: Proactive Foresight and Ethical Mandate
Governance cannot afford to be reactive; it must be anticipatory. A mandatory component of the new framework must be Moral Foresight Planning. This means dedicating resources now to:
- Quantum Transition: Immediate adoption and phased rollout of PQC standards to protect future and historical data from the looming threat of quantum decryption.
- AI Ethics: Developing auditable, transparent governance models for all AI used in law enforcement to prevent algorithmic bias, ensure accountability, and preserve the public’s trust in fair policing.
- Future Threat Modelling: Continuous, formal collaboration with military and intelligence agencies to model and prepare for high-level, state-sponsored cyber-warfare scenarios that target critical national infrastructure, ensuring we are prepared for 'Day Zero' events.
A Final Word
The fight against modern cybercrime is fundamentally a race against time. It’s a defining clash between the rapid and borderless innovation of criminal syndicates and the sluggishness of our outdated institutions. By tolerating this existing institutional latency we’re not just falling behind; we’re actively giving cybercriminals their most potent weapon: the exploitable governance gap.
The solution lies not in isolated technical fixes or temporary security patches but in a comprehensive and systematic structural redesign. The Unified Framework for Structural Cyber Resilience mandates immediate and decisive action from governments and law enforcement agencies. This involves aligning their governance, ethics, and talent strategies with the harsh realities of the digital threat. Transitioning from outdated, siloed, territorial policing to a proactive, globally coordinated and technologically agile governance model is not merely beneficial; it’s absolutely essential for securing our digital future. Embracing this crucial structural imperative is central to the Next Evolution – the only path forward to ensure the rule of law prevails in the digital age.
Key Takeaways: Outpacing the Syndicates
Pillar 1: Sovereign Data Governance: Treating data as a shared national asset to fix interoperability failures between agencies.
Pillar 2: Global Legal Harmonisation: Moving beyond slow MLATs toward automated, judicially sanctioned cross-border data access.
Pillar 3: Adaptive Human Capital: Creating a Cyber Specialist Career Track to stop the "brain drain" from the public sector to private tech.
Pillar 4: Proactive Moral Foresight: Mandating the transition to Post-Quantum Cryptography (PQC) and AI ethical audits today.
Strategic Insights: Beyond Territorial Polciing
Dimension A: Financial Extortion: The rise of Ransomware-as-a-Service (RaaS) and the industrialisation of fraud.
Dimension B: Infrastructure & Espionage: The threat to CNI (Critical National Infrastructure) and state-sponsored information warfare.
Dimension C: Content & Identity: The crisis of authentication triggered by Deepfakes and Algorithmic Crime.
The Evidence Crisis: Why 19th-century jurisdictional boundaries are causing a collapse in digital prosecution.
Video Summary: Fighting a 21st-Century War
The 19th-Century Trap: Why territorial policing is ineffective against borderless, machine-speed syndicates.
Institutional Latency: Defining the hidden cost of bureaucratic delay that acts as a criminal's greatest weapon.
The Quantum Threat: Why the "Quantum Transition" is a mandatory component of future governance.
The Next Evolution: Shifting from reactive investigations to a technologically agile, globally coordinated governance model.
A unified governance strategy is only as strong as the infrastructure it sits upon. Even the best policy fails when intelligence is trapped in departmental isolation. Next, we address the physical barriers: Data Silos.
The Ethical CTO: Arc 2 Index
- The Speed of Change: Governing the Tempo
- Where Policy Fails: The Governance Gap
- The Strategic Bridge: Closing the Gap
- Breaking the Structural Barriers : Data Silos
- The new OS of Society: Governing the Algorithmic State
- The human cost of exclusion: The Algorithmic Abyss
- Designing for Civic Agency: The Ethical Architect
- Trust in the age of AI: Policing at an Inflection Point
- The zenith of converged security: Designing the Future-Ready force